Considering the AI buzz, the models could now even discover software vulnerabilities faster than humans. The future is here, as Microsoft, the tech giant, has made its mark in AI-powered cyber defense. The company has launched a powerful multi-model agentic security system, MDASH short for “multi-model agentic scanning harness.” It’s built by Microsoft Autonomous Code Security System.
It’s a network of specialized AI agents designed to discover bugs in software code end-to-end. It differs from the single-model approach and works as a complete cybersecurity team that handles different vulnerability stages simultaneously. Here’s the announcement made by Satya Nadella regarding the codename MDASH on X.
How Does MDASH Work?
Codename MDASH is mainly an agentic vulnerability and remediation system. It scans software code, confirms findings, and assesses exploitability before reporting vulnerabilities. The system works in five stages as mentioned below:
- Prepare Stage: Builds language-aware indices and then maps the attack surface and threat models by analyzing the past commits.
- Scan Stage: Auditor agents inspect code and vulnerability hypotheses with some supportive evidence.
- Validate Stage: Again, runs the second cohort of agents against every finding to test reachability and exploitability.
- Dedub Stage: Brings together similar vulnerabilities to avoid redundancies.
- Prove Stage: Generates real inputs and proofs of concept exploits to verify the vulnerability.
The Vulnerabilities MDASH Found
The new agentic security system has helped engineering teams find 16 vulnerabilities across the Windows networking and authentication stack using codename MDASH. This also includes-
- Four critical remote code execution flaws
- Windows kernel TCP/IP
- IKEV2 service
Among the 16 vulnerabilities, 10 are kernel-mode, and 6 are user-mode. Most of the vulnerabilities were reachable without credentials. All of these were fixed before Microsoft’s Patch Tuesday release.
Benchmark Speaks!
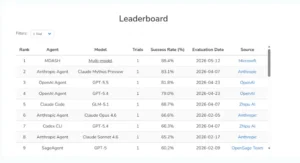
MDASH scored the highest on the leaderboard. It achieved an 88.85% score on the CyberGym benchmark with 1,507 real-world vulnerabilities, outperforming other AI leaders.
- Anthropic Claude Mythos – 83.1%
- Open AI Agent GPT 5.5 – 81.8%
- Claude Code – 68.7%
Source: Microsoft security blog post
Alongside, 21% of 21% planted vulnerabilities found zero false positives on private test drivers.
Why does this Matter?
We are currently in an industry where AI-powered vulnerability discovery is an engineering problem. However, MDASH represents a significant advancement in cybersecurity. AI is evolving from a supporting tool into an autonomous agent capable of discovering and validating vulnerabilities at record speed.
As per the company’s statement, “What we have learned building MDASH and using it across Microsoft is more portable: the harness does the work, and the model is the input.”
Microsoft Security Engineering teams are currently using Codename MDASH. A small set of customers is testing it in a limited private preview, making it a potential foundation for next-generation cyber defense.
To read more trending news updates, head over to our website now!
Recommended For You:
Microsoft to launch Chromium-based browser. Is it the End of Microsoft Edge?
Everything You Need to Know About Microsoft’s LAM: Your Smart Assistant That Gets Things Done